In today’s digital world, businesses are increasingly relying on cloud computing for services like storage, computing power, and applications. While the cloud offers flexibility and scalability, security remains a top concern. This is where Identity and Access Management (IAM) comes into play. IAM is a crucial component of cloud services, enabling organizations to securely manage access to their resources
IAM acts as the digital gatekeeper for your cloud resources. It’s a framework that allows organizations to control who can access what, ensuring only authorized users have the necessary permissions to perform specific actions.
Identity and Access Management (IAM) is an identity service or a tool that helps organizations to securely control access to the infrastructure resources and applications in both on-prem and cloud environments. IAM is used to control who is authenticated (signed in) and authorized (has permissions) to use any resources or applications.
Read: Common mistakes that put DEV accounts at risk
One recent study found that 65% of all cloud security incidents are the result of customer misconfigurations. IAM misconfigurations played a key role in the majority of these incidents along with security related configurations. one simple IAM misconfiguration can allow the whole organization to compromise an entire cloud environment and bypass a full set of security controls. IAM allows organizations to create and manage cloud users and groups, and use permissions to allow and deny their access to resources.
Key Features of IAM:
-
- Shared Access: You can grant others permission to administer and use resources without sharing your own credentials.
- Granular Permissions: Different users can have varying levels of access to different resources. For instance, some may have full access to compute instances, while others might only have read-only access to specific storage buckets.
- Secure Access for Applications: IAM provides credentials for applications running on cloud instances (e.g., Amazon EC2, Azure VMs). These credentials allow applications to securely access other cloud resources like S3 buckets or DynamoDB tables.
- Multi-Factor Authentication (MFA): Enhances security by requiring an additional authentication factor (e.g., a code from a configured device) alongside the usual password or access key.
The above features are common across all the Cloud providers, however each provider has further fine grained IAM controls and permissions defined for each of their cloud services.
By implementing IAM, organizations can:
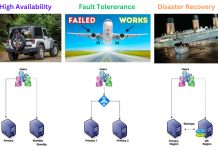
- Minimize security risks: Restricting access based on the principle of least privilege helps prevent unauthorized access, accidental data leaks, and malicious activity.
- Improve compliance: Many regulations require control over user access and data security. IAM facilitates compliance by providing audit logs and clear access control mechanisms.
- Enhance operational efficiency: Centralized management empowers administrators to efficiently manage user access and permissions, saving time and reducing administrative burden.
As a cloud architect understanding IAM is essential to design a solution considering securing the data and resources in the cloud. By implementing a robust IAM strategy, you can confidently embrace the benefits of cloud computing while ensuring the security and compliance of your valuable information.
Cloud IAM vs Traditional Access Management:
While both IAM and traditional access management aim to control access, IAM is tailored for the dynamic, distributed nature of cloud environments, whereas traditional access management is rooted in more localized, on-premises systems. Here are some of the main differences between Cloud based IAM and Traditional IAM tools.
- Scope:
- IAM (Cloud):
- Cloud IAM focuses on managing access to cloud resources (e.g., virtual machines, databases, storage buckets) within a cloud service provider’s environment (e.g., AWS, Google Cloud, Azure).
- It’s tightly integrated with the cloud platform’s services and APIs.
- Traditional Access Management:
- Traditional access management typically deals with on-premises systems, applications, and networks.
- It encompasses user access to physical offices, local servers, and legacy applications.
- IAM (Cloud):
- Location:
- IAM (Cloud):
- Operates in a distributed, global context.
- Users can access resources from anywhere with an internet connection.
- Traditional Access Management:
- Primarily operates within a specific physical location (e.g., an office building).
- Users need to be physically present or connected to the local network.
- IAM (Cloud):
- Authentication Mechanisms:
- IAM (Cloud):
- Supports various authentication methods, including single sign-on (SSO), API keys, and multi-factor authentication (MFA).
- Integrates with external identity providers (e.g., Okta, Azure AD, Google Identity Platform).
- Traditional Access Management:
- Often relies on username/password combinations.
- MFA is less common in traditional setups.
- IAM (Cloud):
- Scalability:
- IAM (Cloud):
- Designed for scalability and elasticity.
- Easily adapts to changing user counts and resource demands.
- Traditional Access Management:
- May struggle to handle sudden spikes in user activity or system load.
- IAM (Cloud):
- Resource Types:
- IAM (Cloud):
- Manages access to a wide range of cloud resources: virtual machines, databases, object storage, etc.
- Traditional Access Management:
- Primarily focuses on access to local servers, file shares, printers, and applications.
- IAM (Cloud):
- Permissions Model:
- IAM (Cloud):
- Uses a policy-based approach for granting permissions.
- Fine-grained control over who can perform specific actions on resources.
- Traditional Access Management:
- Often relies on role-based access control (RBAC).
- Permissions are tied to predefined roles (e.g., admin, user, manager).
- IAM (Cloud):
- Auditability and Logging:
- IAM (Cloud):
- Provides detailed logs and audit trails for resource access.
- Enables tracking of changes and user activity.
- Traditional Access Management:
- Logging capabilities may vary.
- Audit trails are less comprehensive.
- IAM (Cloud):
Authentication vs Authorization
Authentication and authorization, while often used interchangeably, are two distinct but crucial security processes that work together to safeguard your systems and data.
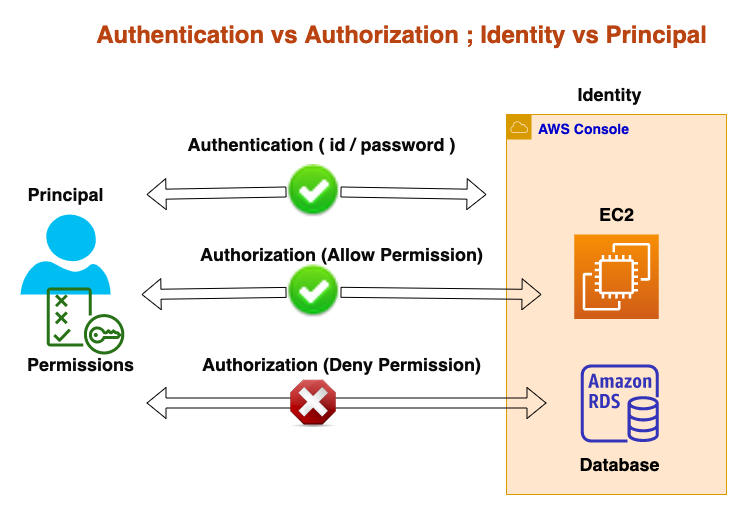
Authentication:
-
- Definition: Authentication is the process of validating that users are whom they claim to be.
- Purpose: It ensures that the user’s identity is genuine before granting access to a system or resource.
- Examples:
- Passwords: The most common authentication factor where users enter correct data (e.g., username and password) to gain access.
- One-time pins: Grant access for a single session or transaction.
- Biometrics: Fingerprint or eye scan verification.
- Multi-factor authentication (MFA): Requires more than one factor for increased security.
- Order: Authentication precedes authorization.
Read: Cloud Computing Quick Reference Guide
Authorization:
-
- Definition: Authorization is the process of granting or denying access to specific resources or functionalities based on the authenticated user’s permissions, roles, or privileges.
- Examples:
- File access: Granting permission to download a specific file on a server.
- Application access: Providing individual users with administrative rights.
- Order: Authorization follows successful authentication.
Combined Security:
Both authentication and authorization work together to establish a robust security posture. Authentication ensures only authorized users attempt access, and authorization defines what they can do once inside.
For example, in a company email system:
- Authentication: Employee logs in with their username and password, verifying their identity.
- Authorization: Based on the employee’s role, the system may grant them access only to their inbox or allow sending and managing emails for others.
By implementing effective authentication and authorization practices, you can create a secure environment while ensuring efficient access control for your users and services.
IAM (Identity and Access Management) vs RBAC (Role-Based Access Control)
IAM (Identity and Access Management) and RBAC (Role-Based Access Control) are two important concepts in cloud security, but they hold different roles. IAM is the big picture, encompassing the entire framework for user identity and access management Whereas RBAC is a specific tool within the IAM framework, focusing on simplifying authorization through pre-defined roles.
IAM can incorporate other access control models besides RBAC, while RBAC often relies on IAM for authentication and other functionalities. Both IAM and RBAC are vital for securing cloud environments, working together to ensure only authorized users have the necessary access level to specific resources.
IAM: The Framework
- Function: IAM is a broad framework encompassing various policies and technologies for managing user identities, access control, and security within a cloud environment.
- Scope: IAM handles the entire process of managing users and their access, including:
- Identity Management: Creating and managing user identities, groups, and roles.
- Authentication: Verifying identities using various methods like passwords, multi-factor authentication, etc.
- Authorization: Defining access control using RBAC and other models, granting permissions based on roles.
- Auditing and Compliance: Tracking user activity, logging access attempts, and ensuring compliance with regulations.
- Example: Imagine IAM as the security guard system in a building. It encompasses all processes: checking IDs (authentication), granting access based on clearance levels (authorization), and keeping track of who enters and exits (auditing).
RBAC: The Tool Within the Framework
- Function: RBAC is a specific access control model used within the larger IAM framework. It focuses on defining roles and assigning them to users or groups, allowing easier permission management.
- Scope: RBAC focuses on the authorization aspect of access control, specifically:
- Defining Roles: Creating specific roles with predefined sets of permissions (e.g., “admin,” “editor,” “reader”).
- Assigning Roles: Granting users or groups specific roles, determining their access level.
- Permission Management: Simplifying access control by managing permissions through pre-defined roles.
- Example: Think of RBAC as the clearance levels in the building security system. Different levels (roles) grant access to specific areas (resources) based on authorized tasks.
Common IAM (Identity and Access Management) policies
As a Cloud architect a thoughtful policy design is essential for maintaining a secure and efficient cloud environment. Regularly review and fine-tune policies to adapt to evolving business needs. Following are some of the commonly used IAM policies to securely manage the cloud, users and applications in any Cloud platform.
- Least Privilege Policy:
- Purpose: The least privilege principle ensures that users and roles have only the minimum necessary permissions to perform their tasks. By granting the least privilege required, organizations reduce the risk of accidental or intentional misuse of resources.
- Implementation:
- Assign specific permissions based on job roles or responsibilities.
- Regularly review and adjust permissions to align with changing requirements.
- Example Scenarios:
- A developer should have read/write access to an S3 bucket but not full administrative rights.
- An analyst needs access to specific database tables but not the ability to modify schemas.
- Administrator Policies:
- Purpose: These policies grant full control over specific services or resources. They are typically assigned to administrative roles responsible for managing the entire environment.
- Implementation:
- Assign policies like AdministratorAccess or FullAccess.
- Use with caution, as these permissions can impact the entire system.
- Example Scenarios:
- An AWS IAM user with AdministratorAccess can manage all AWS services.
- A GCP user with the Owner role has full control over Google Cloud resources.
- Read-Only Policies:
- Purpose: Read-only policies provide access to resources without allowing modifications. These are useful for auditors, monitoring tools, or reporting purposes.
- Implementation:
- Assign policies with read permissions (e.g., ReadOnlyAccess).
- Restrict write or delete actions.
- Example Scenarios:
- An auditor needs to review logs and metrics but should not alter configurations.
- A monitoring tool fetches data from cloud resources without making changes.
- Custom Policies:
- Purpose: Custom policies allow organizations to tailor permissions to specific use cases. They provide fine-grained control over access.
- Implementation:
- Create policies based on business requirements.
- Specify which actions are allowed or denied.
- Example Scenarios:
- A custom policy allowing access to specific EC2 instances for a development team.
- Permissions for a specialized application interacting with specific APIs.
- Cross-Account Access Policies:
- Purpose: These policies facilitate controlled access between different AWS accounts. They enable collaboration across organizational boundaries.
- Implementation:
- Use roles and trust relationships.
- Define which external accounts can assume the role.
- Example Scenarios:
- A development account accessing resources (e.g., S3 buckets, Lambda functions) in a production account.
- Sharing resources securely with partners or third-party vendors.
- Resource-Based Policies:
- Purpose: Resource-based policies control access to specific resources directly. They are attached to the resource itself (e.g., an S3 bucket or an Amazon RDS instance).
- Implementation:
- Specify who can perform actions on the resource.
- Define conditions (e.g., IP addresses, time of day).
- Example Scenarios:
- An S3 bucket policy allowing public read access to specific objects.
- An API Gateway resource policy controlling access to an API endpoint.
- Service-Specific Policies:
- Purpose: These policies focus on individual cloud services (e.g., Amazon RDS, DynamoDB). They provide specialized permissions for specific functionalities.
- Implementation:
- Understand the service-specific actions and resources.
- Assign relevant permissions.
- Example Scenarios:
- A policy granting access to specific tables in DynamoDB.
- Permissions for managing specific Google Cloud Pub/Sub topics.
IAM best practices for a cloud architect
As a cloud architect, implementing robust Identity and Access Management (IAM) practices is crucial for securing your cloud environment. Here are some best practices tailored to your role:
- Implement Strict, Conditional, and Auditable IAM:
- Purpose: Ensure that access controls are well-defined, auditable, and enforced consistently across all users, team members, and system components.
- Implementation:
- Define clear roles and responsibilities for different user groups.
- Leverage IAM policies to enforce fine-grained permissions.
- Regularly audit access logs to detect anomalies or unauthorized actions.
- Limit Access Exclusively to Necessity:
- Purpose: Follow the principle of least privilege. Grant only the permissions required for specific tasks.
- Implementation:
- Avoid granting broad permissions (e.g., AdministratorAccess) unless absolutely necessary.
- Use IAM roles and policies to restrict access based on job responsibilities.
- Use Modern Industry Standards for Authentication and Authorization:
- Purpose: Ensure secure authentication and authorization mechanisms.
- Implementation:
- Implement multi-factor authentication (MFA) for all users.
- Leverage industry-standard protocols (e.g., OAuth, OpenID Connect) for federated identity.
- Rigorously Audit Access Not Based on Identity:
- Purpose: Detect and address any unauthorized access.
- Implementation:
- Regularly review IAM policies and permissions.
- Monitor access patterns and anomalies using AWS CloudTrail or similar services.
- Map Access Privileges to Business Roles:
- Purpose: Align IAM permissions with business functions.
- Implementation:
- Define roles (e.g., developer, administrator, analyst) and associate relevant permissions.
- Avoid over-provisioning by granting only necessary permissions.
- Use IAM Access Analyzer for Least-Privilege Policies:
- Purpose: Automatically generate least-privilege policies based on access activity.
- Implementation:
- Leverage IAM Access Analyzer to validate and refine your policies.
- Ensure that permissions align with actual usage patterns.
- Establish Permissions Guardrails Across Multiple Accounts:
- Purpose: Maintain consistency and security across multiple AWS accounts.
- Implementation:
- Use AWS Organizations to manage accounts hierarchically.
- Define and enforce IAM policies at the organization level.
Remember that IAM is a critical aspect of your cloud architecture. Regularly review and adapt your IAM practices as your environment evolves.