Building a strong foundation for your cloud journey is essential, and that’s where a cloud landing zone comes in. A cloud landing zone is a well-defined, pre-configured cloud environment designed to host your applications and workloads quickly and securely in the cloud. Think of it as the foundation upon which you build your cloud infrastructure, incorporating best practices and essential configurations from the start.
This blog post will guide you through understanding the core building blocks of a cloud landing zone, the unique services offered by major cloud service providers like AWS, Azure, GCP, and Oracle Cloud, and best practices for design and deployment. We’ll also explore important considerations like disaster recovery, data management, cost optimization, and the difference between platform-wide and application-specific landing zones. Whether you’re new to the cloud or looking to optimize your existing environment, this guide will provide valuable insights to ensure your success!
1. Cloud Landing Zone Introduction
The cloud offers unparalleled agility and scalability, but without a solid foundation, your cloud journey can quickly become a security nightmare and a management overhead. Cloud Landing Zone is a pre-configured, secure template that establishes a standardized environment for deploying and managing cloud resources. This guide delves into the technical building blocks of Landing Zones, exploring design considerations, core components, and best practices across leading cloud providers (AWS, Azure, GCP, and Oracle Cloud).
Read: Quick reference guide on AWS Landing Zone Architecture
Read: Quick reference guide on Azure Landing Zone Architecture
-
Beginner’s Explanation: Imagine moving into a new house in a new development. The developer has already established the basic infrastructure – roads, power lines, plumbing – providing a foundation for you to build upon. A cloud landing zone is like that prepped neighborhood for your cloud resources. It gives you a structured starting point with essential security, networking, and management in place.
-
Experienced Engineer’s Explanation: A cloud landing zone is a well-architected environment within a cloud provider’s ecosystem (AWS, Azure, GCP, OCI). It encompasses foundational components like IAM, networking, logging, monitoring, security, and established governance policies.
Why Build a Cloud Landing Zone?
Building a cloud landing zone isn’t just a good idea, it’s a proactive strategy for organizations venturing into the cloud. Here’s why a landing zone becomes your best friend.
-
Large-Scale Cloud Migration: A landing zone provides a structured and secure foundation for organizing and managing a large influx of resources migrating to the cloud.
-
Multi-Account Strategy: If you plan to use multiple cloud accounts for different purposes, a landing zone offers centralized management, simplifying administration and governance.
-
Security & Compliance First: A landing zone enforces security best practices and streamlines compliance by pre-configuring security controls to meet your organization’s requirements.
-
Improved Cost Management: Centralized governance within a landing zone allows you to track and optimize cloud spending across all your accounts.
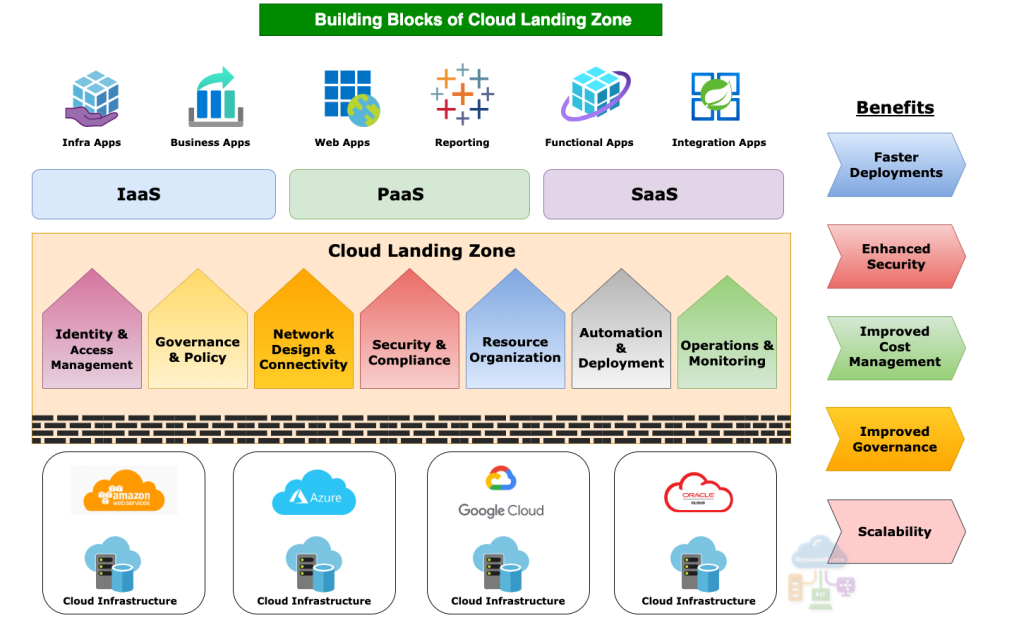
2. Building Blocks of Cloud Landing Zone
A cloud landing zone is essentially a foundation for securely and efficiently deploying workloads in the cloud. Just like any solid foundation, it’s built from key components that provide structure and organization. These building blocks provide a secure and organized foundation for deploying and managing your cloud workloads. The specific configuration of your landing zone will depend on your organization’s unique needs and cloud adoption strategy. Here are the 7 essential building blocks of a cloud landing zone.
Read: Quick reference guide on Google Cloud Landing Zone
Read: Quick reference guide on Google Cloud Landing Zone
-
Identity and Access Management (IAM)
- This building block governs who can access what resources in the cloud environment. It determines which users and groups have permissions to perform specific actions.
- It controls management of
- User directories and identity synchronization.
- Role-based access controls (RBAC).
- Privileged access management.
- Multi-factor authentication (MFA).
-
Governance and Policy
- This building block defines the overall rules and processes for managing the cloud environment. It establishes guidelines for provisioning, configuring, and using cloud resources in a way that aligns with your organization’s security and compliance requirements.
- It provides governance for
- Cost management and optimization policies.
- Security policies and compliance frameworks (e.g., HIPAA, SOC 2, GDPR).
- Naming conventions and tagging standards for resource organization.
-
Network Design and Connectivity
- This building block establishes controls to protect your cloud environment from unauthorized access and malicious activity. Firewalls, Virtual Private Networks (VPNs), and network segmentation are common tools used to create secure network configurations.
- Secure network configurations includes
- Virtual Private Clouds (VPCs) or Virtual Networks (VNets) and Subnets).
- Firewalls and security groups.
- VPNs or dedicated connections for hybrid scenarios.
- Load balancing.
-
Security and Compliance
- This building block emphasizes to create policies and procedures that safeguard your cloud resources from threats. They may include encryption for data at rest and in transit, logging and monitoring, and vulnerability management practices. Implements security controls to protect data, workloads, and the infrastructure from cyber threats.
- Commonly implemented security controls are
- Encryption at rest and in transit.
- Vulnerability scanning.
- Incident response plans.
- Logging and monitoring.
- Compliance auditing.
-
Resource Organization
- This building block establishes a logical structure for managing resources, promoting visibility, and control. This organizes cloud resources in a logical way. It defines a structure for naming conventions, folders, and resource groups to facilitate easy identification, management, and governance.
- Cloud providers have their own way of creating logical structures for managing resources.
- Subscriptions (Azure), Accounts (AWS), Projects (Google Cloud), Compartments (Oracle Cloud)
- Resource groups (Azure), Resource Groups (AWS), Folders (Google Cloud), Tenancy (Oracle Cloud)
-
Automation and Deployment
- This building block prioritizes using automation tools like IaC and CI/CD pipelines to automate provisioning, configuration, and deployment for faster and more error-free rollouts.
- Some common automation tools like
- Infrastructure as Code (IaC) tools (e.g., Terraform, CloudFormation, Cloud Deployment Manager).
- Configuration management tools (e.g., Ansible, Chef, Puppet).
- CI/CD pipelines for automating deployments.
-
Operations and Monitoring
- This building block establishes processes and tools for monitoring the health, performance, and availability of cloud resources. It leverages cloud services for centralized monitoring, logging, alerting, and cost management, enabling proactive issue identification, efficient troubleshooting, and optimized resource utilization.
- Establish cloud services for
- Logging and analysis.
- Alerting.
- Incident management.
- Cost monitoring.
Additional Considerations
In addition to the above core building blocks, a robust cloud landing zone also encompasses several crucial considerations to ensure ongoing operational resilience and data security.
Read: 8 Key design principles to build robust cloud solutions
-
Disaster Recovery & Business Continuity (DR/BC): Focuses on plans and procedures to get critical systems back online quickly after outages or disasters. This minimizes downtime and ensures business continuity.
-
Data Management: Defines strategies for handling your cloud data. This includes storage options, migration plans for moving data to the cloud, data classification for security purposes, and regular backups to prevent data loss.
-
Logging & Auditing: Involves capturing and storing detailed records of activities within your cloud environment. This provides valuable insights for troubleshooting issues, security analysis, and compliance audits.
Benefits of a Well-Defined Cloud Landing Zone
A well-defined cloud landing zone goes beyond just a foundation. It unlocks a range of benefits that streamline operations, enhance security, and optimize costs.
- Agility: Streamlined processes and automation enable faster deployment of new applications and services to the cloud.
- Security and Compliance: Pre-configured security controls and adherence to compliance standards safeguard your cloud environment.
- Scalability: The landing zone’s structure allows for easy scaling of resources up or down to meet fluctuating demands.
- Governance: Standardized configurations and access controls minimize risks and simplify management of your cloud resources.
- Cost Optimization: Centralized monitoring and cost management tools provide better visibility into resource usage, allowing for cost optimization and elimination of wasteful spending.
3. Cloud Landing Zone services offered by AWS, Azure, GCP and OCI
Cloud service providers (CSPs) like AWS, Azure, Google Cloud, and Oracle offer cloud landing zone services to help organizations establish a secure and well-structured foundation for cloud operations. These services generally include blueprints, reference architectures, best practices, and automation tools to quickly set up multi-account environments aligned with security, governance, and compliance requirements. While sharing similarities, they differ in the specific technologies and approaches used. Factors influencing the choice of a landing zone solution include the nature of your workloads, team expertise, integration needs, and cost considerations.
Read: Complete guide on AWS Landing Zone setup
Here’s a quick reference guide for the cloud landing zone building blocks along with the corresponding key services in major cloud providers (AWS, Azure, Google Cloud, Oracle Cloud).
a. Identity and Access Management (IAM)
Identity and Access Management (IAM) is a critical service across all major cloud providers (AWS, Azure, Google Cloud, and Oracle Cloud) that governs user and service access to cloud resources. It typically involves three key functions: authentication (verifying user identities), authorization (determining access rights), and auditing (tracking user activity). Each cloud provider offers its own IAM service with specific tools.
- AWS:
- AWS IAM (Identity Access Management): manages users, roles, and policies.
- AWS SSO (Single Sign-On) for centralized authentication across AWS accounts.
- AWS Secrets Manager for storing and managing credentials.
- Azure:
- Azure Active Directory (Azure AD): identity and access service
- Azure Role-Based Access Control (Azure RBAC): for fine-grained permissions.
- Azure Key Vault: for secrets management.
- Google Cloud:
- Cloud IAM: manages roles and permissions across Google Cloud services.
- Cloud Identity: for identity management and SSO.
- Secret Manager: for storing confidential data.
- Oracle Cloud:
- Oracle Cloud Infrastructure Identity and Access Management (OCI IAM): manages access and permissions.
- Oracle Key Vault: secrets management.
b. Governance and Policy
Governance and Policy is another fundamental aspect of cloud landing zones. It focuses on establishing a set of rules and controls to manage your cloud environment effectively. This includes controlling how resources are created, configured, and used, along with optimizing costs. Major cloud providers offer various tools to achieve this.
Read: The ultimate guide for cloud architects on Cloud Computing services by AWS, Azure, GCP and OCI
- AWS:
- AWS Organizations: for multi-account management with policy hierarchy.
- AWS Service Control Policies (SCPs): enforce cross-account restrictions.
- AWS Config: track and remediate resource configuration changes.
- AWS CloudTrail: for auditing.
- Azure:
- Azure Policy: enforces rules and effects across subscriptions.
- Azure Blueprints: for packaging governance artifacts in templates.
- Azure Resource Manager (ARM): for policy-based deployments.
- Google Cloud:
- Cloud Resource Manager: for organizing resources into a hierarchy.
- Cloud IAM Conditions: fine-grained, context-aware permissions.
- Organization Policy Service: controls use of Google Cloud resources.
- Oracle Cloud:
- OCI Compartments: for logical resource isolation and access control.
- OCI Policies: attach IAM policies to compartments.
c. Network Design and Connectivity
Network Design and Connectivity establishes secure and isolated virtual networks within the cloud environment. These virtual networks mimic traditional networks but exist within the cloud provider’s infrastructure. All major cloud providers (AWS, Azure, Google Cloud, and Oracle Cloud) offer similar functionalities. For example, they all provide a core service to define your virtual network (VPC, VNet, or VCN), along with tools for managing network security, isolation, and communication between resources. Additionally, they offer options for hybrid connectivity, allowing you to securely connect your cloud environment to your on-premises network using VPNs or dedicated connections.
- AWS:
- Amazon VPC (Virtual Private Cloud): for defining your network space.
- AWS Transit Gateway: for interconnecting VPCs & on-premises networks.
- Route 53: DNS service.
- Azure:
- Azure Virtual Network (VNet): building block for private networks.
- VPN Gateways & Azure ExpressRoute: for hybrid connectivity.
- Azure DNS: for domain name resolution.
- Google Cloud:
- VPC (Virtual Private Cloud): foundation for defining your network.
- Cloud VPN & Cloud Interconnect: for hybrid connectivity.
- Cloud DNS: for name resolution.
- Oracle Cloud:
- Virtual Cloud Network (VCN): for network isolation and connectivity.
- OCI FastConnect & IPSec VPN: for hybrid connection options.
d. Security and Compliance
Security and Compliance is paramount for protecting your data, assets, and overall cloud infrastructure. Cloud providers offer a variety of tools and services to implement a layered security approach. This typically involves security controls, monitoring, and threat detection. For instance, all major providers (AWS, Azure, Google Cloud, and Oracle Cloud) offer services like Security Hub, Security Center, or Cloud Guard which centralize security posture management and identify misconfigurations. Additionally, they provide tools like GuardDuty, Sentinel, or Cloud Armor for threat detection and protection against DDoS attacks or web application vulnerabilities.
- AWS:
- AWS GuardDuty: threat detection.
- AWS Security Hub: centralized security management.
- AWS Macie: for sensitive data discovery.
- AWS WAF and Shield: for web application firewalls
- Azure:
- Azure Security Center: unified security posture assessment.
- Azure Sentinel: cloud-based SIEM/SOAR.
- Google Cloud:
- Security Command Center: central security monitoring and management.
- Cloud Armor: DDoS and web application firewall (WAF) protection.
- Oracle Cloud:
- OCI Security Zones: policy-based security.
- OCI Cloud Guard: detects cloud resource misconfigurations.
e. Resource Organization
Resource Organization establishes a structure for managing and controlling your cloud resources. This translates to logically grouping and organizing your resources for efficient administration, cost tracking, and access control. All major cloud providers (AWS, Azure, Google Cloud, and Oracle Cloud) offer functionalities to achieve this. They provide core resource containers (Accounts, Subscriptions, Projects, Tenancy, etc.) that act as the foundation for organization. Additionally, they offer ways to further categorize resources within these containers using tools like Resource Groups or Folders. This layered structure simplifies resource management, billing accountability, and security controls within your cloud environment.
- AWS:
- AWS Accounts: Top-level container for isolating resources and billing.
- AWS Resource Groups: Group resources based on criteria like tags.
- Azure:
- Subscriptions: Connect resources to billing and management boundaries.
- Resource Groups: Logical containers to group resources together
- Google Cloud:
- Projects: Fundamental unit for organizing resources and permissions.
- Folders: Create hierarchies within a Google Cloud Organization.
- Oracle Cloud:
- Compartments: Logical containers for resource isolation and access control.
- Tenancy: The root resource container within your Oracle Cloud account.
f. Automation and Deployment
Automation and Deployment focuses on streamlining the creation, updates, and management of your cloud infrastructure. This eliminates manual configuration and ensures consistency and repeatability through automation. All major cloud providers (AWS, Azure, Google Cloud, and Oracle Cloud) offer various tools and services to achieve this. They all have Infrastructure as Code (IaC) solutions like CloudFormation, ARM templates, or Resource Manager that allow you to define your cloud infrastructure in code.
Additionally, they provide tools for Continuous Integration and Continuous Delivery (CI/CD) such as CodeDeploy, Azure Pipelines, or Cloud Build to automate the build, test, and deployment process for your applications.
Finally, some providers offer services like Systems Manager, Azure Automation, or Cloud Functions for automating specific tasks and configurations within your cloud environment. This automation approach saves time, reduces errors, and ensures consistent deployments across your cloud resources.
- AWS:
- AWS CloudFormation: Infrastructure as Code (IaC) using templates.
- AWS CodeDeploy: Automates application deployments.
- AWS Systems Manager: Configures and manages EC2 & on-premises instances.
- Azure:
- Azure Resource Manager (ARM) templates: IaC in JSON format.
- Azure Pipelines: CI/CD for building and deploying cloud applications.
- Azure Automation: Process automation for tasks and configuration.
- Google Cloud:
- Cloud Deployment Manager: IaC for resource creation and configuration.
- Cloud Build: CI/CD for building, testing, and deploying to Google Cloud.
- Cloud Functions: For event-driven automation.
- Oracle Cloud:
- OCI Resource Manager: IaC using Terraform stacks.
- OCI DevOps: CI/CD tools and services for deployment pipelines.
g. Operations and Monitoring
Operations and Monitoring is crucial for maintaining the health, performance, and visibility of your cloud environment. It allows for proactive management and quick identification of potential issues. All major cloud providers (AWS, Azure, Google Cloud, and Oracle Cloud) offer comprehensive monitoring services. These services typically collect metrics, logs, and other data points from your cloud resources to provide insights into their health and performance. Tools like CloudWatch, Azure Monitor, or OCI Monitoring are central to this function. Additionally, they offer features for log storage, analysis, and visualization through services like Cloud Logging, Log Analytics, or OCI Logging. This combined approach allows you to monitor resource utilization, identify performance bottlenecks, troubleshoot errors, and proactively address potential problems before they impact your cloud workloads.
- AWS:
- Amazon CloudWatch: Logs, metrics, alarms, and dashboards.
- AWS X-Ray: Analyzes and debugs distributed applications.
- AWS Personal Health Dashboard: Personalized status of AWS services.
- Azure:
- Azure Monitor: Collects metrics and logs on Azure resources.
- Azure Log Analytics: For analyzing log data.
- Azure Service Health: Personalized view of Azure service health.
- Google Cloud:
- Cloud Monitoring: Collects metrics and logs.
- Cloud Logging: Log storage and analysis.
- Cloud Trace: Traces application performance and latency.
- Oracle Cloud:
- OCI Monitoring: Collects metrics on OCI resources and applications.
- OCI Logging: Centralized log management system.
4. Other important Cloud Landing Zone Considerations
A secure and well-managed cloud landing zone goes beyond just the core building blocks. To ensure your cloud environment is disaster-proof, data-driven, and cost-efficient, several additional considerations are critical. Think of these as the advanced features that elevate your cloud deployment from functional to exceptional. These include:
h. Disaster Recovery and Business Continuity
Focuses on plans and procedures to get critical systems back online quickly after outages or disasters. The DR plan and procedures should minimize the downtime and quickly recovering your systems and data in the event of disruptions like hardware failures, power outages, natural disasters, or security incidents. This minimizes downtime and ensures business continuity.
- Key Points to consider for planning:
- RPO (Recovery Point Objective): The maximum acceptable data loss in a disaster.
- RTO (Recovery Time Objective): Target time to restore operations after a disruption.
- Backup and Replication: Regular backups and replicating data to different locations/regions are critical.
- Disaster Recovery Plans: Detailed, documented plans that outline the steps to take in case of an outage.
- Cloud Provider Services for DR and Business Continuity:
- AWS: AWS Backup, AWS Site Recovery
- Azure: Azure Site Recovery, Azure Backup
- Google Cloud: Persistent Disk Snapshots, regional/multi-regional replication.
- Oracle Cloud: Oracle Data Guard
i. Data Management
Defines strategies for handling your cloud data. This includes storage options, migration plans for moving data to the cloud, data classification for security purposes, and regular backups to prevent data loss.
- Key Points to consider for Data Migration and Storage:
- Storage Options: Choose from various cloud storage solutions (block, object, databases) based on performance, cost, and access patterns.
- Data Migration: Securely and efficiently transfer data from on-premises locations to the cloud.
- Data Classification: Identify sensitive data and apply appropriate security measures
- Backup & Retention: Set up regular backups and define retention periods to protect against data loss.
- Cloud Provider Services: Cloud providers offer diverse data services across:
- Relational databases (e.g., Amazon RDS, Azure SQL Database, Google Cloud SQL, Oracle Database Service)
- NoSQL databases (e.g., Amazon DynamoDB, Azure Cosmos DB, Google Cloud Firestore, Oracle NoSQL Database)
- Object Storage (e.g., Amazon S3, Azure Blob Storage, Google Cloud Storage, Oracle Object Storage)
j. Logging and Auditing
Involves capturing and storing detailed records of activities within your cloud environment. This provides valuable insights for troubleshooting issues, security analysis, and compliance audits.
- Key Points to consider for Logging and auditing:
- Visibility: Logs provide crucial insights into how your systems are functioning, helping in troubleshooting and performance optimization.
- Compliance: Essential for demonstrating adherence to various industry regulations (e.g., HIPAA, GDPR, PCI DSS).
- Security: Log analysis helps identify anomalies, suspicious activity, and potential security threats.
- Cloud Provider Services for Logging and Auditing:
- AWS: Amazon CloudWatch, AWS CloudTrail
- Azure: Azure Monitor, Azure Log Analytics
- Google Cloud: Cloud Logging, Cloud Operations Suite (formerly Stackdriver)
- Oracle Cloud: OCI Logging, OCI Audit
h. Cost Optimization
Strategies and tools within the landing zone to manage and optimize cloud spending. This includes identifying underutilized resources, setting budgets, and leveraging cost-saving features from your cloud provider. Think of cost optimization as your cloud environment’s financial advisor, ensuring you get the most performance and value from your investment.
- Key Focus Areas
- Right-Sizing Resources: Match your instances and storage to actual usage, avoiding over-provisioning.
- Reserved Instances and Savings Plans: Commit to longer-term usage patterns to secure significant discounts.
- Autoscaling: Automatically add or remove resources to meet fluctuating demand.
- Resource Tagging: Detailed tagging helps pinpoint where costs are accruing.
- Cost Monitoring and Budgets: Set alerts and track spending to stay within desired limits.
- Cloud Provider Services for Cost Optimization
Proactive cost optimization is essential for a healthy landing zone. By combining smart strategies with your chosen cloud provider’s tools, you can control spending while maximizing the value of your cloud deployments.
-
- AWS:
- Amazon EC2 Spot Instances: Utilize unused EC2 capacity for significant cost savings.
- AWS Cost Explorer: Provides detailed cost breakdowns and insights.
- AWS Budgets: Set custom budgets and receive alerts for potential overspending.
- AWS Reserved Instances and Savings Plans: Offer significant discounts for committed resources.
- Azure:
- Azure Reserved Instances: Discounts for upfront commitment to virtual machines.
- Azure Spot VMs: Leverage unused Azure capacity for cost-effective compute.
- Azure Cost Management: Provides cost analysis, recommendations, and optimization options.
- Azure Budgets: Set budgets and receive proactive alerts for potential cost overruns.
- Google Cloud:
- Committed Use Discounts: Discounts for sustained use of specific Google Cloud resources.
- Preemptible VMs: Utilize surplus Google Cloud capacity for cost-effective compute.
- Cloud Billing: Provides detailed cost reports and insights.
- Cloud Billing Budgets: Set custom budgets and receive alerts for potential overspending.
- Oracle Cloud:
- Universal Credit Model: Flexible model for purchasing compute and storage resources.
- Bare Metal Instances: Cost-effective option for specific workloads.
- Cost Management Service: Provides cost analysis, reporting, and optimization recommendations.
- Budgeting and Notifications: Set custom budgets and receive alerts for potential cost overruns.
- AWS:
5. Summary table of the Cloud landing zone services by AWS, Azure, Google Cloud and Oracle Cloud
| Building Block | Key Functions | AWS | Azure | Google Cloud | Oracle Cloud |
|---|---|---|---|---|---|
| Identity & Access Management (IAM) | Authentication, authorization, auditing | AWS IAM, AWS SSO, AWS Secrets Manager | Azure AD, Azure RBAC, Azure Key Vault | Cloud IAM, Cloud Identity, Secret Manager | OCI IAM, Oracle Key Vault |
| Governance & Policy | Resource management rules and controls, cost optimization | AWS Organizations, AWS SCPs, AWS Config, AWS CloudTrail | Azure Policy, Azure Blueprints, Azure Resource Manager | Cloud Resource Manager, Cloud IAM Conditions, Organization Policy Service | OCI Compartments, OCI Policies |
| Network Design & Connectivity | Virtual networks (VPC/VNet/VCN), security, hybrid connectivity | Amazon VPC, AWS Transit Gateway, Route 53 | Azure VNet, VPN Gateway, Azure ExpressRoute, Azure DNS | VPC, Cloud VPN, Cloud Interconnect, Cloud DNS | VCN, OCI FastConnect, IPSec VPN |
| Security & Compliance | Security controls, monitoring, threat detection | AWS GuardDuty, AWS Security Hub, AWS Macie, AWS WAF and Shield | Azure Security Center, Azure Sentinel | Security Command Center, Cloud Armor | OCI Security Zones, OCI Cloud Guard |
| Resource Organization | Logical grouping of resources for management, control, cost tracking | AWS Accounts, AWS Resource Groups | Subscriptions, Resource Groups | Projects, Folders | Compartments, Tenancy |
| Automation & Deployment | Streamlining creation, updates, management with Infrastructure as Code (IaC) | AWS CloudFormation, AWS CodeDeploy, AWS Systems Manager | ARM templates, Azure Pipelines, Azure Automation | Cloud Deployment Manager, Cloud Build, Cloud Functions | OCI Resource Manager, OCI DevOps |
| Operations & Monitoring | Ensuring health, performance, visibility | Amazon CloudWatch, AWS X-Ray, AWS Personal Health Dashboard | Azure Monitor, Azure Log Analytics, Azure Service Health | Cloud Monitoring, Cloud Logging, Cloud Trace | OCI Monitoring, OCI Logging |
| Disaster Recovery & Business Continuity | Plans for restoring operations after outages, minimizing downtime | AWS Backup, AWS Site Recovery | Azure Site Recovery, Azure Backup | Persistent Disk Snapshots, replication | Oracle Data Guard |
| Data Management | Strategies for storage, migration, classification, backups | Amazon RDS, S3, DynamoDB, etc. | Azure SQL Database, Blob Storage, Cosmos DB, etc. | Cloud SQL, Firestore, Cloud Storage, etc. | Oracle Database Service, Object Storage, NoSQL Database, etc. |
| Logging & Auditing | Capturing activities for troubleshooting, security, compliance | Amazon CloudWatch, AWS CloudTrail | Azure Monitor, Azure Log Analytics | Cloud Logging, Cloud Operations Suite | OCI Logging, OCI Audit |
| Cost Optimization | Managing cloud spending, identifying underutilized resources | AWS Cost Explorer, AWS Budgets, EC2 Spot Instances, Savings Plans | Azure Cost Management, Azure Budgets, Reserved Instances, Spot VMs | Cloud Billing, Committed Use Discounts, Preemptible VMs | Universal Credit Model, Cost Management Service, Bare Metal Instances |
6. Cloud Platform Landing Zone vs Application Landing Zone
In a multi-layered cloud deployment, platform and application landing zones work together to establish a secure and efficient foundation. Platform landing zones act as the central hub, offering shared services like authentication and logging for multiple, isolated application landing zones.
Whereas the application landing zones inherit security policies from the platform but maintain specific configurations for their deployed applications. Imagine it as a company headquarters providing core services to its branch stores, each with some level of customization for their unique needs.
Platform Landing Zone: The Secure and Efficient Foundation
- Purpose: Establishes the core infrastructure and services that multiple applications can leverage.
- Key Components:
- Identity and Access Management (IAM): Centralized control over who can access what within your cloud environment.
- Networking: The backbone of communication – virtual networks, firewalls, and connections to other environments.
- Logging and Monitoring: Essential visibility into how your cloud resources are performing.
- Security: Enforces overarching security policies to keep your data protected.
Application Landing Zone: Tailored Environments for Your Workloads
- Purpose: Provides a dedicated space for specific applications or groups of related applications.
- Inherits the Foundation: Application landing zones benefit from the security and governance established by the platform landing zone.
- Room for Customization: Includes:
- Application-Specific Resources: Storage, databases, and computing power optimized for your workloads.
- Tailored Security: Additional controls to match the sensitivity of your application’s data.
- Focused Monitoring: Track metrics relevant to the performance of your applications.
Platform landing zones create a solid, secure base. Application landing zones enable you to deploy your applications efficiently and tailor their environments to maximize performance – all within the secure boundaries defined by your platform landing zone.
7. Best Practices for Cloud Landing Zone Design and Deployment:
To build a secure, scalable, and well-managed cloud foundation, prioritize these best practices across all core building blocks of your landing zone. Employing these guidelines will strengthen your identity and access management, governance, networking, security, automation, and operations, leading to a truly successful cloud deployment. Here’s a breakdown of best practices for cloud landing zones organized by their key building blocks:
1. Identity and Access Management
(IAM)
- Least Privilege Principle: Grant only the minimum necessary permissions to users and services.
- MFA Everywhere: Enforce multi-factor authentication for all critical actions and privileged access.
- Centralized Identity Management: Use a single directory/provider for authentication and authorization.
- Fine-Grained Access Control: Leverage Role-Based Access Control (RBAC) for precise permission management.
- Audit and Review: Periodically audit IAM roles, permissions, and user activity.
2. Governance and Policy
- Policy as Code: Define governance rules as code (e.g., AWS Config, Azure Policy) for automated enforcement.
- Standardization and Templates: Create reusable templates and blueprints to ensure consistency and best practices.
- Clear Documentation: Maintain a comprehensive and up-to-date documentation of policies and standards.
- Change Management: Implement a structured change management process to track and review resource changes.
3. Network Design and Connectivity
- Defense in Depth: Utilize a layered security approach with firewalls, subnets, and security groups.
- Segmentation: Isolate different environments and workloads based on their sensitivity and access requirements.
- Least Exposure: Minimize publicly exposed resources and use security best practices (e.g., bastion hosts).
- Hybrid Connectivity (if needed): Establish secure connections between your cloud and on-premises networks.
- Centralized Traffic Inspection: Route traffic through inspection points for monitoring and threat detection.
4. Security and Compliance
- Data Encryption: Protect data at rest and in transit using strong encryption standards.
- Vulnerability Management: Regularly scan for vulnerabilities and apply patches promptly.
- Threat Detection and Response: Implement tools and processes for detecting and responding to security incidents.
- Compliance Alignment: Map your landing zone design to applicable standards (e.g., SOC 2, HIPAA, PCI DSS).
- Regular Audits and Reviews: Conduct regular security audits and penetration tests.
5. Resource Organization
- Logical Structure: Create a hierarchy (e.g., projects, subscriptions, resource groups) for organizing and managing resources.
- Meaningful Tagging: Use tags for cost tracking, resource identification, and automation.
- Multi-account Strategy (if needed): Use separate accounts for development, testing, and production environments, or to enforce isolation.
6. Automation and Deployment
- Infrastructure as Code (IaC): Use tools like Terraform, CloudFormation, or ARM templates for consistent and repeatable deployments.
- CI/CD Pipelines: Automate the testing, building, and deployment of infrastructure and application code.
- Configuration Management: Maintain a consistent configuration state and mitigate configuration drift with tools like Ansible, Chef, or Puppet.
7. Operations and Monitoring
- Centralized Logging: Aggregate logs from across your cloud resources for troubleshooting and analysis.
- Proactive Monitoring: Implement real-time monitoring of resource health, performance, and security metrics.
- Alerting and Thresholds: Define clear thresholds and generate alerts for critical events or deviations.
- Incident Response: Have documented incident response plans and conduct regular drills.
8. Disaster Recovery & Business Continuity
- Define RPO and RTO: Clearly establish your recovery point and recovery time objectives to guide your disaster recovery plan.
- Replication Strategies: Choose the right data replication methods (e.g., asynchronous, synchronous, multi-region) based on your RPO and RTO requirements.
- Failover and Failback: Design processes for automatic or manual failover to a secondary site, and procedures to return to normal operation (failback).
- Regular Testing: Test your DR plans under simulated conditions to identify gaps and ensure procedures work as expected.
9. Data Management
- Data Classification: Categorize data based on sensitivity (e.g., confidential, public) and apply appropriate security controls.
- Data Lifecycle Management: Define policies for data storage, retention, archival, and secure disposal.
- Migration Planning: If migrating from on-premises, develop a phased plan with tools and processes to minimize disruption.
- Choose the Right Storage: Select storage services (block, object, file) based on performance requirements, access patterns, and cost considerations.
10. Logging and Auditing
- Centralize Log Collection: Aggregate logs from all cloud resources into a centralized system for analysis.
- Retention Policies: Implement log retention based on compliance requirements and your analysis needs.
- Security Use Cases: Design log collection and analysis to support security incident detection and forensics.
- Compliance Alignment: Ensure logging practices meet the audit requirements of applicable regulations.
11. Cost Optimization
- Right-Sizing Resources: Match instance types and storage sizes to your workload needs, avoid overprovisioning.
- Reserved Instances/Savings Plans: Take advantage of discounts for long-term commitments if usage is predictable.
- Autoscaling: Dynamically add or remove resources based on demand to avoid paying for unused capacity.
- Spot Instances: Leverage unused cloud capacity with spot instances or preemptible VMs for suitable, non-critical workloads.
- Monitoring and Budgeting: Use your cloud provider’s cost analysis and alerting tools to track spending and stay within budget thresholds.
Additional best practices considerations
- Leverage Cloud-Native Services: Utilize managed services offered by your cloud provider when possible to reduce operational overhead.
- Training and Awareness: Educate teams on cloud best practices, security protocols, and cost-saving measures.
- Cloud Provider Specific Guidance:Always refer to the best practices and reference architectures provided by your chosen cloud provider.
Conclusion:
Prioritize standardization, security, and automation for successful landing zone management. Develop reusable templates for IAM, networking, and tagging to ensure consistency and simplify administration. Embed security throughout your design with strong authentication, least privilege access, and continuous monitoring. Automate as much as possible with Infrastructure as Code (IaC) tools to reduce errors, boost deployment speed, and maintain consistency. Finally, implement comprehensive monitoring to proactively track security threats, resource usage, and cost optimization opportunities.
Remember: Adapt and Iterate! Cloud technologies and best practices evolve. Review your cloud landing zone regularly and adapt to optimize it over time. These best practices should always be adapted to your organization’s specific needs, risk tolerance, and compliance requirements.
8. Advanced Cloud Landing Zone Design Considerations:
Advanced cloud landing zone design takes your cloud deployment to the next level, focusing on enhanced security, granular controls, and complex workload support. Here’s a breakdown of key advanced cloud landing zone considerations:
Read: GenAI Basics and Fundamentals
-
Multi-Cloud/Hybrid Environments: Designing for seamless integration between on-premises systems and different cloud providers (AWS, Azure, Google Cloud, etc.). This often involves:
- Consistent networking and connectivity across environments.
- Centralized identity management spanning multiple providers.
- Governance and policy harmonization.
-
Zero Trust Architecture: Implementing the principle of “never trust, always verify.” This strengthens security by:
- Requiring strong authentication for all access.
- Employing micro-segmentation to limit the blast radius of breaches.
- Continuously monitoring for anomalous activity.
-
Fine-Grained Access Controls: Moving beyond simple role-based access to implement context-aware authorization. Consider:
- Attribute-based access control (ABAC) for dynamic permissions based on user attributes, resource properties, and environmental factors.
- Time-limited access or just-in-time privilege escalation.
-
DevSecOps Automation: Integrating security deeply into your CI/CD pipelines for continuous vulnerability scanning, automated policy checks, and remediation.
-
Resiliency and Chaos Engineering:
- Proactively testing your architecture’s ability to withstand failures through controlled experiments.
- Leveraging fault injection tools to uncover weaknesses.
-
Containerization and Microservices: Designing landing zones optimized for containerized workloads (Kubernetes, Docker) including:
- Service meshes for traffic control and security between microservices.
- Orchestration platforms for managing container lifecycles.
-
Edge Computing: Extending your landing zone to support edge workloads where data processing occurs close to its source. This requires:
- Distributed deployment and management mechanisms.
- Security strategies tailored for edge devices.
-
AI and Machine Learning: Incorporating considerations for hosting and managing ML workloads, such as:
- Data preparation and storage solutions.
- Supporting large-scale compute and GPU demands.
- Ensuring governance and ethical usage of AI.
Important Notes: Tailor your landing zone design to the unique demands of your specific applications, ensuring it adequately supports their complexities. Additionally, stay informed about emerging cloud technologies like blockchain, IoT, and serverless, incorporating relevant services and best practices into your landing zone to maintain its adaptability and cutting-edge capabilities.
Advanced landing zone design goes beyond the foundational elements to address complex scenarios like multi-cloud or hybrid environments, zero-trust security, fine-grained access controls, and DevSecOps automation. It incorporates strategies for resilient architectures tested through chaos engineering, containerization and microservices support, edge computing capabilities, and responsible AI/ML workload management. To support these advanced use cases, it’s essential to align your landing zone design with specific workload complexities and stay informed about emerging cloud technologies.
9. Summary and Conclusion
Summary and key takeaways:
- Landing zones provide a centralized foundation for deploying, managing, and securing your cloud resources.
- Core landing zone components include identity and access management, networking, logging and monitoring, security baselines, and resource organization.
- Major cloud providers offer various landing zone services, from IAM and security tools to cost management and resource optimization features.
- Consider additional factors like disaster recovery, data management, and logging & auditing when designing your landing zone.
- Platform landing zones provide shared infrastructure and services, while application landing zones cater to specific application needs.
- Best practices for design and deployment include planning, collaboration, focusing on security and compliance, automation, and ongoing monitoring.
- Advanced considerations like multi-account strategies, fine-grained access control, and network segmentation further enhance your cloud environment.
By implementing these insights, you can leverage cloud landing zones to create a secure, efficient, and scalable foundation for your cloud journey.
Conclusion:
A cloud landing zone is much more than simply setting up an account in the cloud. A well-designed landing zone is the cornerstone of successful cloud adoption. By carefully considering the core building blocks – identity management, governance, network design, security, resource organization, automation, and operations – you create a solid base for your applications.
Cloud providers like AWS, Azure, GCP, and OCI offer a rich array of services tailored towards building a robust landing zone. Remember, success also involves proactive attention to disaster recovery, data management, logging and auditing, and cost optimization.
As your cloud environment grows, a distinction between platform-level and application-specific landing zones will help you manage complexity. Prioritizing best practices throughout the design and deployment process ensures you start with a secure, scalable, and cost-effective foundation.
For truly advanced use cases, look into strategies like multi-cloud or hybrid environments, zero-trust security models, containerization, and integrating AI/ML workloads. Your landing zone should remain adaptable, continuously evolving with new technologies and best practices.
The cloud journey is often best traveled together! Whether you’ve conquered a cloud landing zone challenge or are seeking guidance on a specific aspect, our community is here to help. Share your victories, find solutions to roadblocks, and learn from the experiences of others. Let’s spark meaningful conversations – leave your cloud landing zone success stories or questions in the comments below6