There are different backup methods which can be used to backup the organization’s application and their data. Below are the majorly used backup methods in the current IT industry.
Data Backup Methods
Hot Backups
In the modern IT world, almost all backups are hot backups. Hot backups are also referred as online backups. They are known as online backups because backups are taken while the application and server being backed up remain online and servicing users. Hot backups are ideal for today’s demands on IT resources, where servers and applications are expected to remain up and online 24/7. Hot backups also help reduce administrative overhead and allow backup environments to scale because they don’t require administrative stops and restarts of applications to be coordinated and managed to run the backups.
Most modern applications, such as Oracle Database, Microsoft SQL Server, Microsoft Exchange Server, Microsoft SharePoint Server, SA and Vmware etc all support hot backups. IBM TSM offers Tivoli Data Protect for Applications and Databases to take the online/hot backups. To provide this hot-backup feature, most applications place themselves into a hot-backup mode and utilize some form of point-in-time (PIT) technology that creates a frozen image of application data. This frozen image is then used for the backup. Quite often, snapshot technologies, including array-based snapshot technologies, are utilized as part of the PIT frozen image creation process. Another matter of extreme importance in the world of hot backups is the ability to perform integrity checks against backups. Additionally, most good applications that support hot backups have robust facilities to perform checksums, application-based integrity checks, and verification’s of backup images. Doing this helps ensure that the backup is a good backup and will be useful as an image to restore from.
Offline Backups
Offline Backups are the opposite of online/hot backups and these are sometimes referred as cold backups. Offline backups require applications and databases to be taken offline for the duration of the backup. This type of backup method is not ideal if the the organization runs 24/7 and cannot afford downtime of applications and services while performing regular backups.
LAN-Based Backups
LAN based backup method is the traditional backup method and it is still used by many organizations because of its inexpensive and convenient. It offers low performance with a risk of impacting other traffic on the network. LAN based backups works by sending backup data over the LAN and this LAN can be a dedicated backup LAN or shared along with the production LAN. In a typical LAN-based backup configuration, the backup client will send data from the server being backed up over the LAN to the storage media.
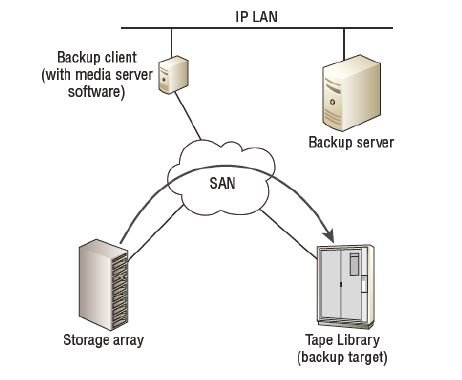
LAN-Free Backups (SAN-based backups)
Unlike LAN-based backups, a LAN-free backups uses SAN infrastructure (FC Channel) to send the backup from the host to the storage media. LAN-free backups offers high performance and reliability but at a higher cost. If you have large data to be back up and you have small backup window, LAN-free backup method can be used to finish the backups within backup window. In this backup method, the client being backedup has direct connectivity to a SAN-based tape library through FC medium. In order to achieve this, you need a agent software that can talk directly to a tape library . The backup server tells the agent software on the backup client to perform a backup to the tape library backup target. The backup data is then sent directly to the tape library over the SAN rather than the LAN. This will reduce the load on the LAN and it will use the FC SAN technology to deploy a robust high performance backup environment without having to deploy a dedicated backup LAN. In IBM TSM, the agent software is referred as TSM Storage Agent.
In a Virtual environment, the agent software running on the server consumes CPU cycles and memory resources. If multiple VMs on a server are backed up simultaneously, then the combined I/O and bandwidth demands placed on the compute system by the various backup operations can deplete the compute system resources. This may impact the performance of the services or applications running on the VMs. To overcome these challenges, the backup process can be offloaded from the VMs to a proxy server. This can be achieved by using the image-based backup approach.
Serverless Backups
Serverless backups are a form of LAN-free backup, they are not only LAN free but also server free. They do not use the server resources for taking the backup. Serverless backups use the SCSI based EXTENDED COPY command, which allows data to be copied directly from a source LUN to a destination LUN without passing through the server that owns the data.
Network Data Management Protocol (NDMP) Backup
NDMP is a protocol designed for efficient NAS backups. It is similar to serverless backups where the data can be sent directly from the NAS device to the backup device without having to pass through a backup media server. As the amount of unstructured data continues to grow exponentially, organizations face the daunting task of ensuring that critical data on NAS systems are protected. Most NAS heads run on proprietary operating systems designed for serving files. To maintain its operational efficiency generally it does not support the hosting of third-party applications such as backup clients. This forced backup administrators to backup data from application server or mount each NAS volume via CIFS or NFS from another server across the network, which hosted a backup agent. These approaches may lead to performance degradation of application server and production network during backup operations, due to overhead.
Further, security structures differ on the two network file systems, NFS and CIFS. Backups implemented via one of the file system would not effectively backup any data security attributes on the NAS head that was accessed via a different file system. For example, CIFS backup, when restored, would not be able to restore NFS file attributes and vice-versa. These backup challenges of the NAS environment can be addressed with the use of Network Data Management Protocol (NDMP).
NDMP is an industry-standard TCP/IP-based protocol specifically designed for a backup in a NAS environment. It communicates with several elements in the backup environment (NAS head, backup devices, backup server, and so on) for data transfer and enables vendors to use a common protocol for the backup architecture. Data can be backed up using NDMP regardless of the operating system or platform. NDMP backs up and restores data without losing the data integrity and file system structure with respect to different rights and permission in different file systems. Due to its flexibility, it is no longer necessary to transport data through the application server, which reduces the load on the application server and improves the backup speed. NDMP optimizes backup and restore by leveraging the high-speed connection between the backup devices and the NAS head. In NDMP, backup data is sent directly from the NAS head to the backup device, whereas metadata is sent to the backup server.
The key components of an NDMP infrastructure are NDMP client and NDMP server. NDMP client is the NDMP enabled backup software installed as add-on software on backup server.
The NDMP server has two components: data server and media server. The data server is a component on a NAS system that has access to the file systems containing the data to be backed up. The media server is a component on a NAS system that has access to the backup device. The backup operation occurs as follows:
- Backup server uses NDMP client and instructs the NAS head to start the backup.
- The NAS head uses its data server to read the data from the storage.
- The NAS head then uses its media server to send the data read by the data server to the backup device
In this backup operation, NDMP uses the production network only to transfer the metadata. The actual backup data is either directly transferred to backup device (NDMP 2-way) or through private backup network (NDMP 3-way), by the NAS head.
- NDMP 2-way (Direct NDMP method) – In this method, the backup server uses NDMP over the LAN to instruct the NAS head to start the backup. The data to be backed up from the storage is sent directly to the backup device. In this model, network traffic is minimized on the production network by isolating backup data movement from the NAS head to a locally attached backup device. During the backup, metadata is transferred via NDMP over the LAN to the backup server. During a restore operation, the backup server uses NDMP over the LAN to instruct the NAS to start restoring files. Data is restored from the locally attached backup device.
- NDMP 3-way (Remote NDMP method) – In this method, the backup server uses NDMP over the LAN to instruct the NAS head to start backing up data to the backup device attached to NAS head. These NAS devices can be connected over a private backup network to reduce the impact on the production LAN network. During the backup, the metadata is sent via NDMP by the NAS head to the backup server over the production LAN network. NDMP 3-way is useful when there are limited backup devices in the environment. It enables the NAS head to control the backup device and share it with other NAS heads by receiving backup data through NDMP.
Direct Primary Storage Backup
This backup approach backs up data directly from primary storage system to a backup target without requiring additional backup software. Typically, an agent runs on the application servers that control the backup process. This agent stores configuration data for mapping the LUNs on the primary storage system to the backup device in order to schedule backup and recovery operations. This backup information (metadata) is stored in a catalog which is local to the application server. When a backup is triggered through the agent running on application server, the application momentarily pauses simply to mark the point in time for that backup. The data blocks that have changed since the last backup will be sent across the network to the backup device. The direct movement from primary storage to backup device eliminates the LAN impact by isolating all backup traffic to the SAN. This approach eliminates backup impact on application servers and provides faster backup and recovery to meet the application protection SLAs.
For data recovery, the backup administrator triggers recovery operation, then the primary storage reads the backup image from the backup device. The primary storage replaces production LUN with the recovered copy.